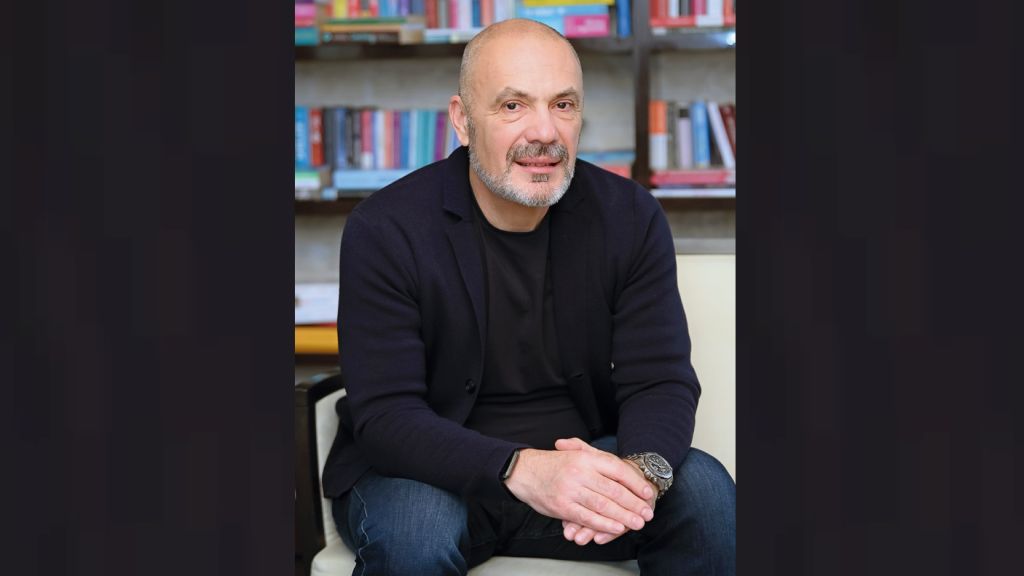
Valeriu Nistor: In the Digital Era, the large volumes of data are generated with high speed from an entire variety of information sources. In order to combat frauds and cyber attacks in an efficient manner in terms of cost and implementation, IBM recently introduced comprehensive new security software and services to help organizations protect their critical data in an environment where advanced persistent threats, zero day attacks, breaches and the financial impact on an organization continue to rise. Through pervasive behavioral analytics and deep research expertise, IBM can help organizations stop attackers from exploiting these vulnerabilities.
According to studies conducted by Ponemon Institute, the average cost of a data breach increased by 15 percent globally, reaching an average of USD 3.5mn. The majority of companies surveyed say targeted attacks are the greatest threat, costing them on average USD 9.4mn in brand equity alone.
The launch of IBM Threat Protection System and Critical Data Protection Program represent two years of significant investment in organic development and the acquisition of companies, including Q1 Labs, Trusteer, Guardium, Ounce Labs, Watchfire and Fiberlink/MaaS360. Since forming a dedicated cyber security business in late 2011, IBM has risen to become one of the largest players in enterprise security and has achieved six straight quarters of double-digit growth. According to IDC’s Software Tracker, IBM significantly outpaced the overall security software market, and has moved from the 4th largest security vendor to the 3rd for 2013.
IBM Threat Protection System can help prevent attacks – before they produce any damages. The new system goes beyond traditional signature-based defenses and firewalls to disrupt attacks across the entire attack chain. Organizations are increasingly turning to IBM to help them build a truly comprehensive and intelligent approach to quickly identify and stop advanced threats before they do damage’, mentioned Valeriu Nistor.
Clients testing the IBM Threat Protection System have seen quick results. For example, a health care provider with thousands of endpoints immediately found dozens of instances of malware present, despite their use of many more traditional security tools. This malicious code could be used to remote control endpoints or exfiltrate data, but instead was instantly disabled. Likewise a large European bank recently tried this capability and was able to disable undetected malware across the enterprise.
The IBM Threat Protection System is supported around the world by IBM’s managed security operations centers (SOC), which can monitor the system once deployed by clients. IBM’s SOC Optimization consultants can also deploy and integrate them into customer SOCs.
One of the newest launches in the area of cyber security is IBM Trusteer Apex, software that protects endpoints – from PCs, to smartphones, tablets - the devices that are most susceptible to malware. This product leverages security intelligence and behavioral analytics to go beyond traditional anti-virus approaches and firewalls to disrupt attacks across the entire attack chain. The Trusteer Apex endpoint protection software blocks attempts by cyber criminals to exploit vulnerabilities on the endpoint that can lead to data breaches. It also provides an easy to deploy automated threat analysis capability to prevent attacks.
‘IBM’s security portfolio provides the security intelligence to help organizations holistically protect their people, data, applications and infrastructure. IBM offers solutions for identity and access management, security information and event management, database security, application development, risk management, endpoint management, next-generation intrusion protection and more. IBM operates one of the world’s broadest security research and development, and delivery organizations. IBM monitors 15 billion security events per day in more than 130 countries and holds more than 3,000 security patents’, added Valeriu Nistor. IBM helps thousands of clients address the challenges of securing their people, data, applications and infrastructure.